Zero Trust Security: Twelve Essential Tenets of Zero Trust Security
The advent of zero trust security principle, why it became popular and 12 salient features of it
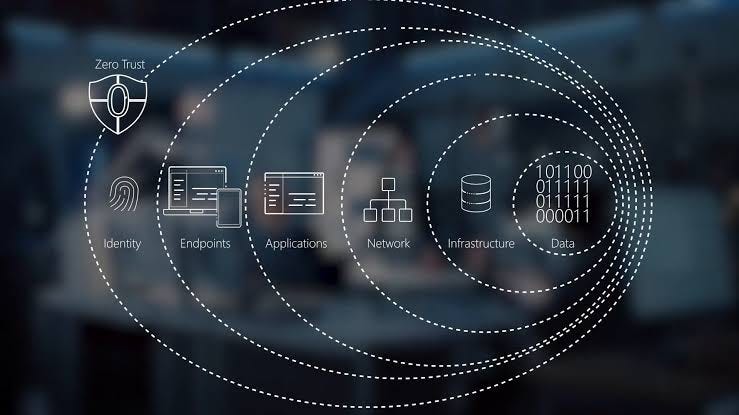
Understanding Zero Trust Security
Introduction
“Trust should never be assumed and always needs verification” that is the baseline thought of Zero Trust Security. This principle changes the definition of trust in the digital realm. It leverages on the tools that help the organization for:
identity verification,
enforces the principle of least privilege,
emphasizing continuous monitoring and data encryption.
Threats originate from anywhere. It might be external or internal. The core philosophy of zero trust structure is rigorous verification and least privileged access.
Understanding Zero Trust Security
The age old perimeter level defenses might not be enough for evolving cybersecurity. The rise of cloud based application and mobile workforce needs different paradigm of digital security.
Rigorous Identity Verification
Zero Trust demands that every user and device is rigorously authenticated. Implementation methodologies may include multi-factor authentication (MFA), strong password policies, and even behavioral analytics to ensure that individuals or systems identification and verification.
Principle of Least Privilege
The concept of least privilege is central to Zero Trust. It means that access rights and permissions are minimized, granting individuals or devices only the essential access required to perform their tasks. This reduces the attack surface and limits potential damage in case of a breach.
Network Segmentation
Network segmentation involves dividing one big network into smaller, isolated segments. Each segment has its access controls and security policies, preventing lateral movement of threats within the network.
Continuous Monitoring
Zero Trust is not a one-time setup; it's a continuous process. Systems and user behavior are continually monitored to detect anomalies or suspicious activities. This real-time analysis is essential for identifying and responding to potential threats.
Data Encryption
All data, whether in transit or at rest, should be encrypted. This ensures that even if a breach occurs, the data remains unreadable and confidential.
The 12 Essential Tenets
Verify Identity: It emphasizes the rigorous verification of user and device identities. It often involves features like multi-factor authentication (MFA) to confirm that the entity seeking access is legitimate.
Least Privilege Access: Grant users and devices only the minimum level of access and permissions required to perform their specific tasks. This principle minimizes the potential attack surface by limiting unnecessary access.
Micro-Segmentation: It is basically process of dividing the whole access segments (teams/entities in an organisation) into isolated segments or micro-segments. Each micro-segment has its own access controls, reducing the ability of threats to move laterally within the network.
Continuous Monitoring: Continuous monitoring of user and device behavior is essential for spotting anomalies and potential threats in real-time. It is a proactive approach to identify and respond to suspicious activities.
Data Encryption: To protect data from unauthorized access, encryption is applied to data both in transit and at rest. Even in the event of a breach, the data remains encrypted and confidential.
Access Control Policies: Access control policies are essential in determining who can access specific resources, under what circumstances, and for how long. These policies are often enforced through centralized management.
Network Security Segmentation: Internal network segmentation isolates different applications, services, and data. This reduces the lateral movement of attackers, limiting their ability to navigate within the network.
Continuous Security Assessment: Regular security assessments, including vulnerability scanning and patch management, are vital to identify and rectify potential weaknesses and vulnerabilities within the system.
User and Device Trustworthiness: The trustworthiness of both users and devices is continuously evaluated. This can include checking the health and security posture of devices and assessing user behavior for signs of compromise.
Security Analytics: Advanced analytics and machine learning are used to detect emerging threats and anomalies. This proactive approach helps in the early identification and mitigation of security risks.
Policy Automation: The automation of access control policies and security measures ensures consistent and real-time enforcement, reducing the potential for human error.
User Education: Educating users about security best practices and their role in maintaining security is essential. Informed users are a critical component of a successful Zero Trust model.
Why Zero Trust Matters
Following are the reasons why zero trust matters:
Evolving Threat Landscape: Cyber threats are evolving at an alarming pace. Attackers are becoming more sophisticated and persistent. The perimeter-based security approach was designed for a different era and is no longer sufficient to protect against modern threats. Zero Trust acknowledges that threats can originate from anywhere and at any time.
Remote Workforce: The rise of remote work has dispersed the workforce, making it challenging to secure access from various locations and devices. Zero Trust enables organizations to secure access regardless of the user's location.
Cloud and Third-Party Services: With the adoption of cloud services and third-party applications, sensitive data often resides beyond the traditional network perimeter. Zero Trust ensures data protection and access control in these diverse environments.
Insider Threats: Insider threats, whether malicious or unintentional, pose a significant risk. Zero Trust's principle of least privilege and continuous monitoring helps organizations detect and mitigate these threats effectively.
Data Protection and Compliance: Many industries are subject to strict data protection regulations. Zero Trust helps organizations maintain data integrity and confidentiality, which is essential for compliance with regulations like GDPR, HIPAA, and CCPA.
Resilience Against Breaches: While no security model can guarantee 100% protection, Zero Trust is designed to limit the damage in case of a breach. By compartmentalizing network segments and implementing rigorous access controls, it reduces the lateral movement of threats.
Advanced Persistent Threats (APTs): APTs are stealthy, long-term cyberattacks that often target high-value assets. Zero Trust's continuous monitoring and security analytics are well-suited to detect these persistent threats early.
Digital Transformation: As organizations undergo digital transformation, Zero Trust offers a flexible and adaptive security framework that aligns with evolving business needs.
Client and Customer Trust: Security breaches erode client and customer trust. Implementing Zero Trust is a proactive way to demonstrate a commitment to data protection, enhancing the organization's reputation.
Cost of Breaches:
Data breaches can result in significant financial losses, legal liabilities, and reputational damage. Zero Trust helps minimize these costs by reducing the potential impact of security incidents.
Implementing Zero Trust
The key steps in implementing the zero trust security system in an org includes:
Assessment and Planning:Evaluate your current environment.Identify critical assets.
Data Classification:Label data based on sensitivity.
Identity and Access Management (IAM):Implement MFA and SSO.Apply least privilege access.
Micro-Segmentation:Divide the network into segments.Define access controls for each.
Continuous Monitoring:Use real-time monitoring and alerts.
Data Encryption:Encrypt data in transit and at rest.
Access Control Policies:Specify who can access what resources.
Network Security Segmentation:Isolate network segments.
Continuous Security Assessment:Regularly test and address vulnerabilities.
User and Device Trustworthiness:Continuously evaluate trustworthiness.
Security Analytics:Use analytics to detect threats.
Policy Automation:Automate policy enforcement.
User Education:Educate employees about security.
Change Management:Implement changes gradually.
Testing and Validation:Regularly test your implementation.
Incident Response Plan:Prepare for security incidents.
Adaptability:Be flexible and adapt to evolving threats.
Tools and Technologies
Implementing Zero Trust Security requires a combination of tools and technologies to enforce access control, continuously monitor the network, and maintain the principles of least privilege. Here's an overview of the key tools and technologies used in Zero Trust implementations:
Identity and Access Management (IAM):
- Microsoft Azure Active Directory: Provides robust identity management and access control for Microsoft-centric environments.
- Okta: Offers identity and access management solutions, including Single Sign-On (SSO) and Multi-Factor Authentication (MFA).
- Ping Identity: Specializes in identity and access management solutions for modern applications.
2. Firewalls and Network Segmentation:
- Next-Generation Firewalls (NGFW): Such as Palo Alto Networks and Cisco Firepower, provide network segmentation, application visibility, and threat prevention.
- Software-Defined Networking (SDN): Technologies like VMware NSX enable network segmentation and micro-segmentation.
3. Micro-Segmentation:
- VMware NSX: Allows for micro-segmentation of virtual networks to control traffic between individual workloads.
- Illumio: Offers adaptive micro-segmentation to prevent lateral movement of threats within the network.
4. Continuous Monitoring and Security Analytics:
- Splunk: Provides real-time security monitoring and analytics to detect and respond to threats.
- Cisco Stealthwatch: Offers network visibility and behavioral analytics for threat detection.
5. Data Encryption:
- Microsoft BitLocker: Encrypts data on Windows devices, ensuring data-at-rest security.
- SSL/TLS: Transport Layer Security protocols for encrypting data in transit.
6. User and Device Trustworthiness:
- Cisco Identity Services Engine (ISE)**: Evaluates the trustworthiness of devices and enforces security policies.
- Cisco SecureX: Provides comprehensive security analytics and threat response.
7. Policy Automation:
- Cisco Application Centric Infrastructure (ACI): Automates network and security policy enforcement.
- F5 BIG-IP: Offers policy enforcement and traffic management capabilities.
8. Security Information and Event Management (SIEM):
- IBM QRadar: Aggregates and analyzes log and event data for threat detection.
- ArcSight: Delivers SIEM and security analytics for advanced threat detection.
9. Endpoint Security:
- CrowdStrike: Provides endpoint protection with AI-driven threat detection and response.
- Carbon Black: Offers endpoint security and threat hunting capabilities.
10. Cloud Security:
- Netskope: Cloud security platform for data and threat protection in the cloud.
- Zscaler: Cloud-native security platform for secure internet access.
11. User Education and Awareness:
- Employee training programs to enhance cybersecurity awareness and best practices.
These are the tools and awareness activities that are required to create an environment and infrastructure favorable to implement zero trust security
Future Trends in Zero Trust
Following are the future trends in the Zero Trust Security infrastructure
Zero Trust as a Standard: In the coming years, Zero Trust is likely to become the standard approach to cybersecurity. More organizations will adopt its principles to protect their networks and data.
Convergence of Zero Trust and SASE: Zero Trust principles will merge with Secure Access Service Edge (SASE) solutions. This convergence will provide secure access for remote and mobile users to applications, regardless of their location.
AI and Machine Learning Integration: The use of artificial intelligence (AI) and machine learning will increase in Zero Trust implementations. These technologies will improve threat detection, automation, and adaptive access controls.
User and Entity Behavior Analytics (UEBA): UEBA will play a more significant role in identifying anomalies and threats by analyzing user and entity behavior. This will lead to more proactive threat detection and response.
Device Trustworthiness Assessment: The assessment of device trustworthiness will become more sophisticated. Continuous monitoring of devices' health and security posture will be central to Zero Trust.
Data-Centric Security: Zero Trust will increasingly focus on data-centric security, where the protection of data is paramount. Encryption, data classification, and data loss prevention will be key elements.
Blockchain for Identity Verification: Blockchain technology may be used for identity verification and access control, enhancing trust in the authentication process.
Software-Defined Perimeters (SDP): SDPs will become more popular for enforcing Zero Trust policies. SDPs enable secure, on-demand access to resources without exposing them to the broader network.
API Security: With the growing use of APIs in modern applications, API security will be a significant concern. Zero Trust principles will extend to API access and protection.
Security Automation and Orchestration: Automation and orchestration will be critical for enforcing Zero Trust policies in real-time and responding to threats.
Regulatory Compliance: Zero Trust will align with evolving data protection regulations, such as the European Union's ePrivacy Regulation and the California Privacy Rights Act (CPRA).
User Privacy Protection: As organizations collect more data for user behavior analysis, privacy protection will be a priority. Implementing Zero Trust without compromising user privacy will be a challenge.
Zero Trust for IoT: Internet of Things (IoT) devices will become more integrated into Zero Trust networks, requiring robust security measures for these often vulnerable devices.
Threat Intelligence Sharing: Collaboration on threat intelligence among organizations and industries will enhance the ability to respond to threats effectively within a Zero Trust framework.
Evolving Threats: Zero Trust will adapt to emerging threats, including quantum computing threats and AI-driven cyberattacks.
Conclusion
Zero Trust Security is essential in today's digital world. It verifies access and adapts to evolving threats. Embracing Zero Trust enhances cybersecurity, protects data, and ensures resilience in a changing threat landscape.